Creating an SBOM is foundational for supply chain security, alongside open-source governance and securing the infrastructure as code elements that touch applications throughout the SDLC. That box is


Creating an SBOM is foundational for supply chain security, alongside open-source governance and securing the infrastructure as code elements that touch applications throughout the SDLC. That box is

Kubernetes clusters, as well as containers in general, are vulnerable as entry points for intruders seeking to orchestrate ransomware attacks, due largely to their highly distributed nature. With these privileges required to
Two common types of AST when shifting left are software composition analysis (SCA) and static application security testing (SAST). There are a number of forms of application security testing (AST) that aim to detect

For SaaS in particular, there are a set of best practices CISOs can implement that can help companies embrace digital transformation and balance their risk management policies with the business objectives.

This post presents an approach that you can apply at scale to achieve fine-grained access controls to resources in S3 buckets and Amazon Redshift schemas for tenants, including groups of users belonging to the same business unit down to the individual user level. T

For example in Azure, a security team using a VM may have that identity at least privilege, but then higher up in the RBAC model, at the management group level, it was set that all devs in the application group

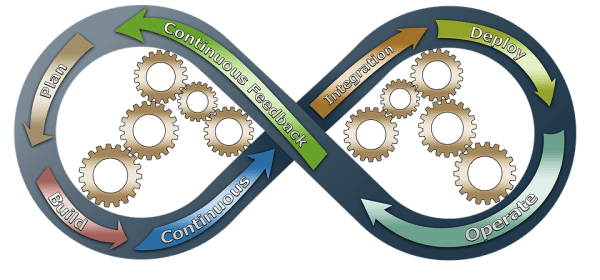
This means you need to secure CI/CD pipelines, your container orchestrator, and the way you build your microservices. Their purpose is exactly that: securely storing secrets in your Kubernetes so you don’t need to pass them in

Presently, cloud-native security is experiencing changes and innovations that help address security threat vectors. These areas are of significant importance for security professionals, software developers, and information technology specialists.

Zero trust security is a paradigm that leverages identity for access control and combines it with contextual data, continuous analysis, and automated response to ensure that the only network resources accessible to users and devices are those explicitly authorized for consumption. Cloud security and

Reachability and risk have dramatically shifted in recent years as we have moved from a hard perimeter “fortress” approach to security to more distributed systems, APIs, cloud computing, SaaS and far more potential points for attack ingress and exfiltration egress. Contemplation is what will

You can also go a step further and integrate a third-party cloud security platform like Sonrai Dig into your environment for automatic identity relationship monitoring. Dig automatically identifies and maps data in the Azure cloud, enabling security teams to view and manage location and

And this week, three tech companies joined forces to offer a free suite of products to help keep smaller enterprises safe, under the umbrella of the Critical Infrastructure Defense Project . While yes, ransomware attacks can

In part two, we have included the top security logs to monitor by cloud platform: Google Cloud, Amazon Web Services and Microsoft Azure. Sadly, cloud providers haven’t necessarily simplified this journey for customers

Zero-trust is a framework and approach to security that assumes an organization’s IT assets — software, networks, data — are constantly at risk and must be secured through continuous verification of the identity, and the