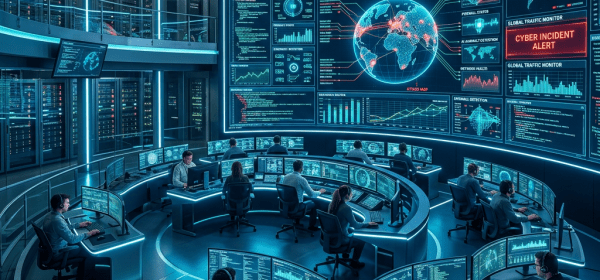
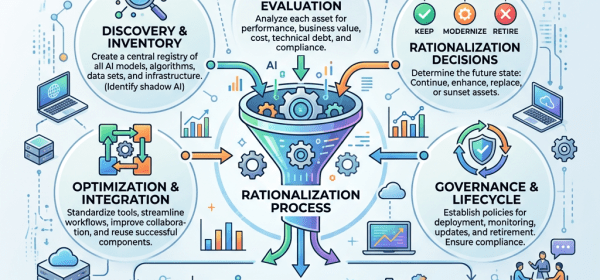
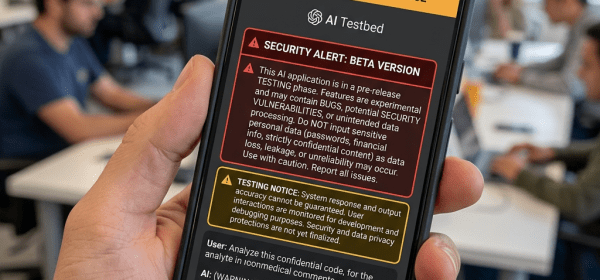
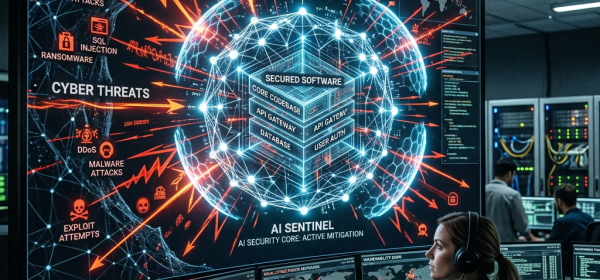
Current discussions around AI are dominated by unrealistic fears of superintelligence and human displacement, while immediate safety concerns are overlooked. The Global Index for AI Safety indicates a drastic increase in AI incidents, highlighting a gap in effective governance. Absolute AI containment is impossible; a shift to adaptive risk management is essential for realistic safety.