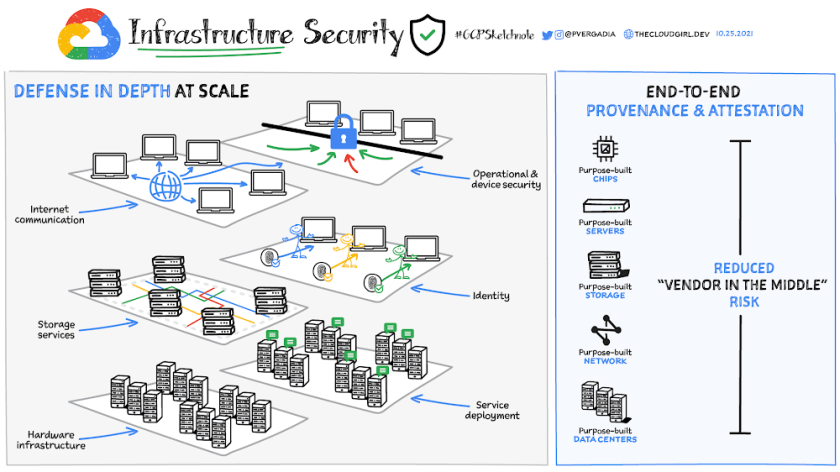
The security of the infrastructure that runs your applications is one of the most important considerations in choosing a cloud vendor. Google Cloud’s approach to infrastructure security is unique. Google doesn’t rely on any single technology to secure its infrastructure. Rather, it has built security through progressive layers that deliver defense in depth.
Defense in depth at scale
- Data center physical security – Google data centers feature layered security with custom-designed electronic access cards, alarms, vehicle access barriers, perimeter fencing, metal detectors, biometrics, and laser beam intrusion detection. They are monitored 24/7 by high-resolution cameras that can detect and track intruders. Only approved employees with specific roles may enter.
- Hardware infrastructure – From the physical premises to the purpose-built servers, networking equipment, and custom security chips to the low-level software stack running on every machine, the entire hardware infrastructure is controlled, secured, and hardened by Google.
- Service deployment – Any application binary that runs on Google infrastructure is deployed securely. No trust is assumed between services, and multiple mechanisms are used to establish and maintain trust. Google infrastructure was designed from the start to be multitenant.
- Storage services – Data stored on Google’s infrastructure is automatically encrypted at rest and distributed for availability and reliability. This helps guard against unauthorized access and service interruptions.
- User identity – Identities, users, and services are strongly authenticated. Access to sensitive data is protected by advanced tools like phishing-resistant security keys.
- Internet communications – Communications over the internet to Google cloud services are encrypted in transit. The scale of the infrastructure enables it to absorb many denial-of-service (DoS) attacks, and multiple layers of protection further reduce the risk of any DoS impact.
- Operational and device security – Google operations teams develop and deploy infrastructure software using rigorous security practices. They work to detect threats and respond to incidents 24 x 7 x 365. Because Google runs on the same infrastructure that is made available to Google Cloud customers, all customers directly benefit from this security operations and expertise.
End-to-end provenance and attestation
Google’s hardware infrastructure is custom-designed “from chip to chiller” to precisely meet specific requirements, including security. Google servers and software are designed for the sole purpose of providing Google services. These servers are custom built and don’t include unnecessary components like video cards or peripheral interconnects that can introduce vulnerabilities. The same goes for software, including low-level software and the server OS, which is a stripped-down, hardened version of Linux.
Further, Google designed and included hardware specifically for security. Titan, for example, is a purpose-built chip to establish a hardware root of trust for both machines and peripherals in cloud infrastructure. Google also built custom network hardware and software to improve performance and security. This all rolls up to Google’s custom data center designs, which includes multiple layers of physical and logical protection.
Tracking provenance from the bottom of this hardware stack to the top enables Google to control the underpinnings of its security posture. This helps Google greatly reduce the “vendor in the middle problem”; if a vulnerability is found, steps can be immediately taken to develop and roll out a fix. This level of control results in greatly reduced exposure for both Google Cloud and its customers.
That was a bird’s eye view of Google Cloud infrastructure security and some services that help protect your infrastructure in Google Cloud. For a more in-depth look into this topic check out the whitepaper.
For more #GCPSketchnote, follow the GitHub repo. For similar cloud content follow me on Twitter @pvergadia and keep an eye out on thecloudgirl.dev
Enjoyed this article? Sign up for our newsletter to receive regular insights and stay connected.